A single pentest gives you a snapshot. Continuous Penetration Testing gives you ongoing coverage — recurring monthly reviews that combine AI-assisted discovery with expert manual analysis, tracking your security posture as your product and infrastructure evolve.
We offer two variants depending on what you need to cover. One is focused on your external internet-facing assets and attack surface. The other is focused on your SaaS platform or web application at the application layer. Both use AI tooling to expand coverage and speed — but every finding is validated by a human before it reaches you.
Recurring reviews and manual testing of everything exposed externally under your domain. We assess what is visible from the internet — subdomains, services, open ports, login panels, cloud-exposed assets — and surface validated findings as part of each review cycle.
Best for: companies with multiple public-facing services or a broad external infrastructure that changes frequently.
Periodic security reviews of your SaaS product or web application at the application layer — authenticated and unauthenticated. We review access control, business logic, APIs, session handling, and new features as your product evolves month by month.
Best for: SaaS startups and growing software teams that want ongoing application-level security coverage without commissioning a full pentest each time.
Both variants start at $200/month · AI-assisted, expert-validated · Billed monthly · 3-month minimum
Variant 1
We perform AI-assisted recurring reconnaissance of your public attack surface throughout the engagement period, then manually validate every finding before delivery. No noise. No false alarms. Just the findings that matter.
AI-powered reconnaissance identifies subdomains and newly exposed assets under your main domain as part of each review cycle, building an updated picture of your external exposure that improves over time.
We assess exposed ports and services as part of each review cycle, identifying newly enabled services, unexpected exposure, and configuration changes since the previous assessment.
We identify cloud-exposed assets, public login panels, and common misconfigurations that create real attack vectors against your external perimeter.
AI tooling runs continuous checks and flags anomalies. Our team then performs manual analysis periodically each month, with special focus on critical changes and findings that require human judgment.
Every reported vulnerability is manually reviewed before delivery. No automated reports, no noise — only verified, actionable findings reach you.
When a review surfaces a high-severity finding, we escalate it through the platform without waiting for the end of the review cycle. All findings are manually validated before being communicated.
Variant 2
Periodic security reviews of your SaaS product or web application — authenticated and unauthenticated — at the application layer. AI-assisted tooling accelerates discovery across access control, business logic, APIs, and new features. Every finding is expert-validated before delivery.
We review your platform monthly from both perspectives — as an anonymous user and as authenticated users with different roles — catching issues at every access level.
We focus on the vulnerabilities that matter most for SaaS products: broken access control, IDOR/BOLA, privilege escalation, sensitive data exposure, and logic flaws in critical workflows.
We test the API endpoints used by your platform — REST and GraphQL. Authorization, session tokens, input handling, and endpoint access control are all in scope.
As your product evolves, we focus periodic reviews on new features, changed workflows, and sensitive areas. Clients can share release notes or changelogs — but the service does not require heavy monthly involvement from your team.
The same team reviews your platform every month. Over time, we build a detailed understanding of your product logic and history — which makes each subsequent review more effective than starting from scratch.
We track whether fixed issues stay fixed. If a vulnerability resurfaces after a deployment, we catch it. Revalidations can be requested directly from the platform at any time.

Manual pentests are valuable — but for products that evolve continuously, recurring testing creates compounding benefits that a one-off assessment cannot provide.
The same team reviews your environment month after month. We learn your product logic, architecture, and sensitive flows — making each subsequent review more effective than starting from scratch.
A pentest done in January is partially outdated by March. Continuous testing means your security posture is evaluated on an ongoing basis — not just once or twice a year.
Fixed vulnerabilities sometimes reappear after a refactor, a new deployment, or a dependency update. Continuous testing catches regressions before they become incidents.
No need to scope, quote, and commission a full traditional pentest every quarter. The service runs continuously with low overhead on your side. You get findings when there are findings.
SaaS products that ship weekly cannot wait for annual assessments. Continuous testing keeps pace with how modern products are actually built and deployed.
We use AI-assisted tooling to improve discovery and coverage — but every finding is reviewed and validated by a human before it reaches you. No automated false alarms.
You want visibility across your full external exposure — domains, subdomains, services, internet-facing assets. You are concerned about misconfigurations, newly exposed services, or assets you may not know exist. Your infrastructure is broad or evolves frequently.
You have a SaaS product or web application and want recurring security coverage at the application layer. You care about access control, business logic, authenticated flows, and API security. You want new features reviewed as they ship — not six months later.
Many teams benefit from both — or start with one and add the other as their needs grow. Send us a message and we will help you identify which variant makes more sense for your current situation and risk profile.
Yes. If you want complete coverage — external surface visibility plus ongoing application-level testing — we can scope a combined engagement. Contact us for a custom proposal.
Both variants are billed monthly and start from $200/month. Pricing is scoped to your environment — we run a brief initial analysis and send you a tailored proposal within 24 hours.
To get started, just send us your main domain. If you are interested in the Web Platform variant, you can optionally include access to a staging environment. No lengthy process, no commitment before you see the proposal.
3-month minimum commitment. Discounted semi-annual and annual prepayment options available.
Request a ProposalPublic Attack Surface focuses on your external internet-facing infrastructure — subdomains, exposed services, misconfigurations. Web Platform focuses on your actual SaaS application — authenticated and unauthenticated testing at the application layer, covering access control, business logic, APIs, and new features.
For the Public Attack Surface variant: just your main domain. For the Web Platform variant: your domain plus access to a staging or production environment. No internal data or source code required for either.
We typically begin with a broader initial review of the full platform, then continue with periodic monthly reviews focused on new features, changed workflows, and sensitive areas. Clients can optionally share release notes or changelogs, but this is not required every month.
Hours are defined during scoping and depend on the size and complexity of your environment. A portion is always reserved for unplanned changes and findings that require prompt escalation.
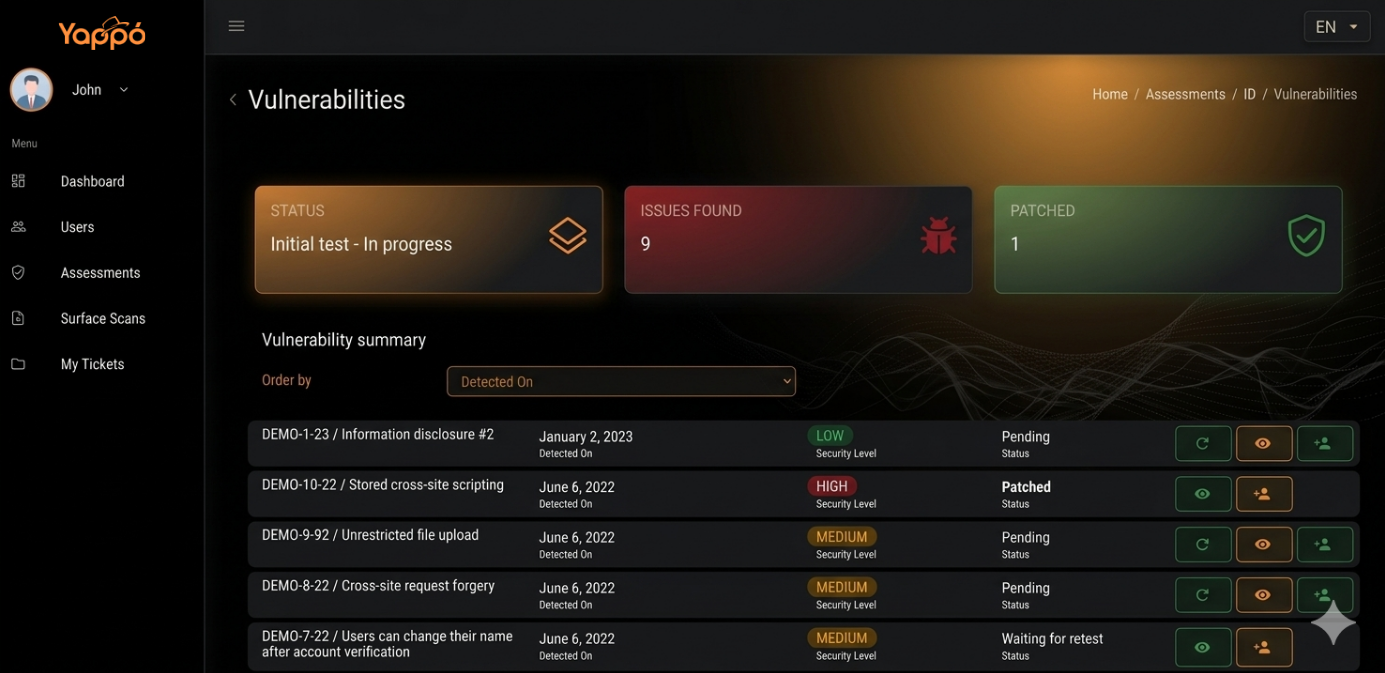
Validated findings are loaded into the Yappo CyberSec Platform, where you can sort by severity, status, and date. High-severity findings are escalated promptly through the platform without waiting for the end of the review cycle. All findings include full evidence and remediation guidance.
No. For the Public Attack Surface variant, recurring reconnaissance activities are automated — but all analysis and validation is performed manually. For the Web Platform variant, testing is hands-on and expert-led throughout. AI-assisted tooling improves coverage but does not replace human judgment.
Request a free initial evaluation and receive a tailored proposal based on your exposed attack surface.
Contact Us